OpenVPN is a client and server VPN implementation that runs on multiple platforms. It establishes a virtual network over a channel secured by TLS. In 2020, you would expect it to support the latest TLS protocol. Well, no. But we can fix that (at least on Windows).
Update: On April 17, version 2.4.9 was released with an up-to-date OpenSSL that supports TLS 1.3. The current tutorial is still useful to update the OpenSSL library of OpenVPN that may get outdated. As a matter of fact, a security fix for OpenSSL (v1.1.1g) was released just 4 days after the latest OpenVPN release, which remains unpatched as of May 2nd, 2020 unless you proceed to update the library.
OpenVPN and OpenSSL versions
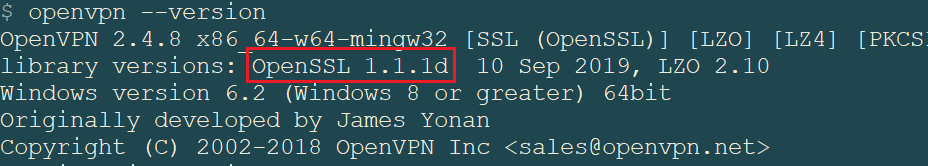
The latest version of OpenVPN for Windows as of February 2020 is v2.4.8 and was released on October 31st, 2019.
In v2.4.5 (April 2018), the support for TLS 1.3 (finalized in August 2018) was already visible from the changelog:
Add support for TLS 1.3 in --tls-version-{min, max}
In v2.4.7, the support was clearly advertised: “One of the big things is enhanced TLS 1.3 support.“, one can read.
However, if you proceed to download and install OpenVPN for Windows (either the Win7 or Win10 installer), you will find that it comes with older OpenSSL DLLs. Namely, with v1.1.0l that was released in September 2019.
If you are not familiar with OpenSSL versions, you should know that several branches are maintained in parallel.
- v1.0 is the oldest branch still supported. It does not and will never support TLS 1.3.
- v1.1.0 is a more recent branch that changed a lot of internal stuff, and the API is incompatible with earlier versions. Switching from v1.0 to v1.1.0 requires some code changes in the application. However, this branch does not support TLS 1.3 yet. The good thing is that it’s been made in such a way that an application compatible with this version can simply upgrade to v1.1.1 with no code rewrite needed.
- v1.1.1 is just v1.1.0 with the added support for TLS 1.3.
Why does OpenVPN not include OpenSSL v1.1.1? You may wonder when was this version of OpenSSL released? Well, that was back in September 2018! So I really don’t see any reason why they would package a version of OpenSSL dated from 2019 but from the v1.1.0 branch. Like, why??
One notable advantage of using TLS 1.3 with OpenVPN, is that when your server runs with mutual authentication, the client certificates are sent to the server in an encrypted form and are no longer in plaintext on the wire. That means someone passively looking at your traffic (e.g., airport’s WiFi hotspot, ISP), may no longer recognize you are Alice or Bob based on your certificate. I think that’s already a good plus for privacy, and there is no reason you shouldn’t benefit from it right now.
I complained about this on Twitter, but didn’t get a reply from @OpenVPN.
Let’s fix it
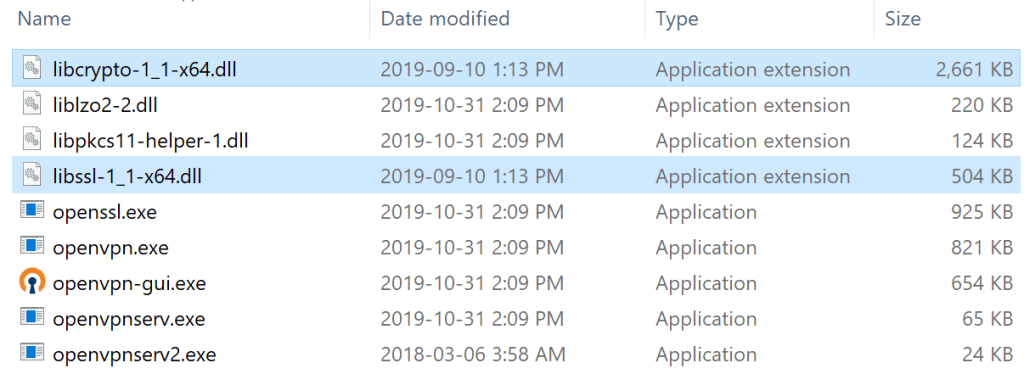
OpenVPN bundles OpenSSL as DLLs, meaning you can replace the OpenSSL component without touching the OpenVPN executable. In %ProgramFiles%\OpenVPN\bin, you can find the two OpenSSL DLLs: libssl-1_1-x64.dll and libcrypto-1_1-x64.dll.
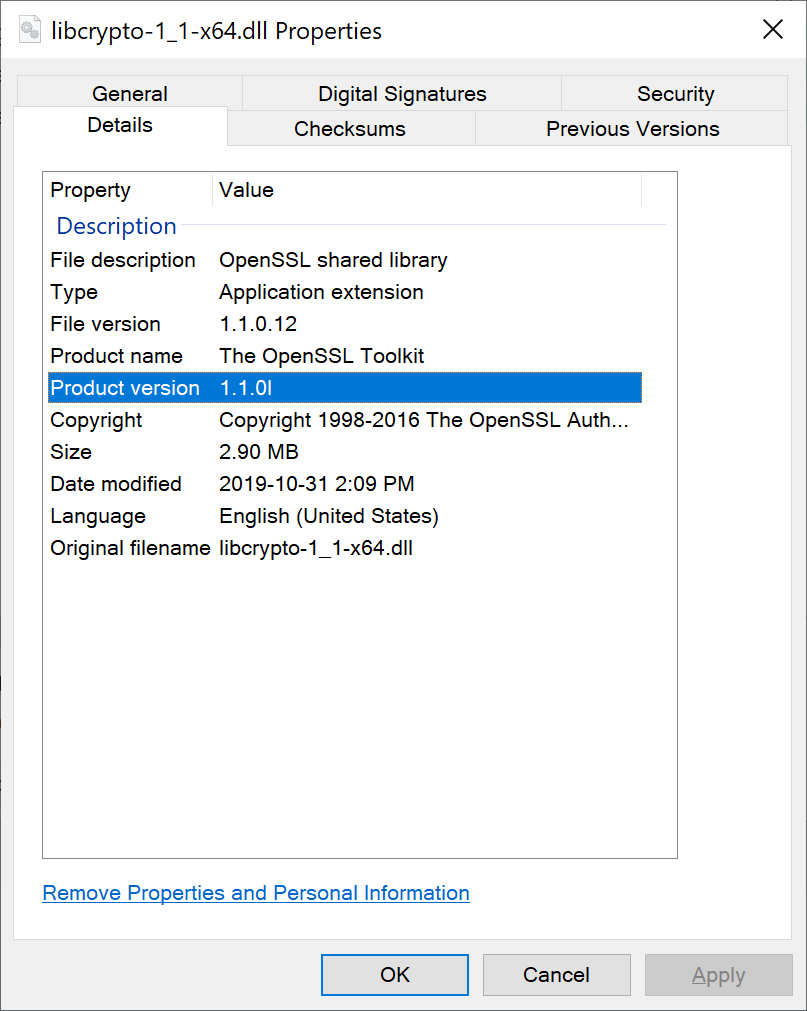
Going to the properties of these files, you can see the outdated version of OpenSSL.
Now, we want to replace these DLLs with more recent ones from the v1.1.1 branch. The most paranoid solution would be to download the source code from openssl.org and compile it ourselves. This is not the easiest solution, though. More realistically, I like OpenSSL’s wiki suggestion of a third-party that provides reproducible builds: https://bintray.com/vszakats/generic/openssl.
Go and download the latest version in the v1.1.1 branch, today would be openssl-1.1.1d-win64-mingw.zip. Identify the two DLLs in the archive and overwrite the ones in OpenVPN’s installation folder. You should end up with something like this (note that the replaced DLLs are older, as indicated from the “Date modified” column): compiled earlier, but from a newer version, that is.
Verify the properties of the newer DLLs:

You may now (re)start OpenVPN, and enjoy a version of OpenSSL that lets you negotiate TLS 1.3 with a server (if compatible).
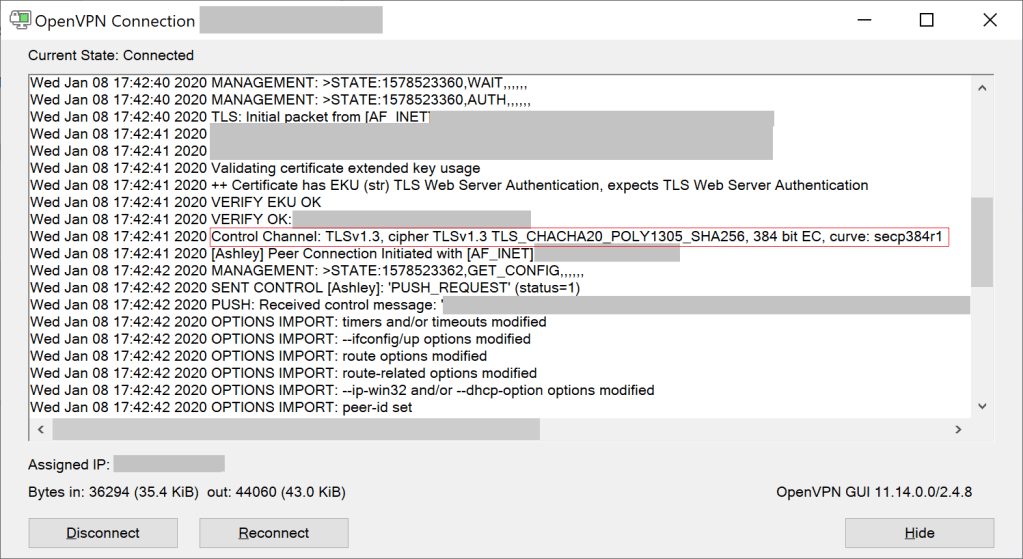
Voilà! Don’t forget to keep OpenVPN up-to-date, and if it still doesn’t come with the right version of OpenSSL, re-do this step again.
The Android OpenVPN app is also stuck at TLS 1.2, but I haven’t figured out a way to fix it. If you have one, please let me know.
In another post, I will go over a proper configuration for OpenVPN server, because there are plenty of misleading and outdated beliefs on this topic.